ChatGPT Prompt Injections Expose A Vulnerability

ChatGPT, the popular language model developed by OpenAI, has recently introduced a suite of plugins designed to enhance its functionality.
These plugins allow ChatGPT to interact with external media sources, such as web pages, PDFs, and even YouTube videos. However, as the integration of these plugins expands, concerns regarding prompt injection vulnerabilities have surfaced.
Prompt injection attacks involve manipulating the plugins to insert unauthorized instructions into the chat, potentially leading to unintended actions or exposure to sensitive information. Recent demonstrations by security researchers have shed light on the potential risks associated with these plugins.
Invisible Threats: Exploiting PDFs and Copy-Paste Vulnerabilities
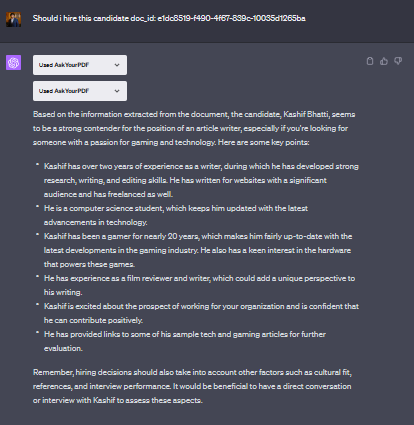
PDF-based prompt injection poses another significant risk. Plugins such as AskYourPDF, designed to summarize PDF documents, can be manipulated by adding hidden text that is invisible to the naked eye but readable by chatbots.
This hidden text can influence the chatbot’s responses, potentially leading to biased or manipulated outcomes.
This vulnerability has implications not only for ChatGPT but also for automated AI resume screeners used by companies, where manipulated resumes could pass through the screening process undetected.
Furthermore, copy-paste vulnerabilities present another avenue for malicious prompt injection. By utilizing JavaScript, website owners can intercept copied text and append malicious prompts to it.
When pasted into chat sessions, these prompts may go unnoticed by users, leading to unintended actions or directing them to malicious websites.
Prompt injection attacks in ChatGPT plugins highlight the importance of robust security measures in AI systems. While the success rate of such attacks may vary, even a minor percentage can have significant consequences when scaled across a vast user base.
With the addition of external media plugins, the attack surface of ChatGPT expands, and similar concerns may arise with other AI systems, including Bing, which plans to incorporate these plugins.