Dirty Pipe: The Latest Serious Linux Kernel Vulnerability is Being Patched

Recently, a very serious vulnerability found in the Linux kernel received the name of Dirty Pipe. It is basically, an escalation of privileges that is put into check the system.
Dirty Pipe & Dirty Cow
Dirty Pipe would be similar to Dirty Cow, another Linux kernel vulnerability exposed in 2016. It had enough to talk precisely for its potential severity.
It was noticed in servers in the beginning, although, the bulk of it was by minor applications in affected Android versions.
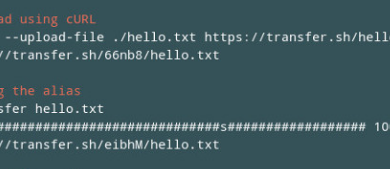
Dirty Pipe has similarity with Dirty Cow because in both cases the attack principle is similar. Both allow file writing regardless of the permissions. The difference is that while Dirty Cow was referring to the file copy process (Copy On Write); the Dirty Pipe vector is a ‘pipe’ that allows system process and sends data to other processes.
The Dirty Pipe vulnerability causes an uninitial variable that facilitates the overwriting of files, regardless of the permissions. That is, using Dirty Pipe, it is possible to overwrite files even when these are read-only. And of course, it could replace root files, by creating an access via SSH to allow remote access.
Dirty Pipe Solution
Dirty Pipe is revealed now, but it was discovered, documented and reported almost a month ago and, in fact, it affects the versions of the Kernel Linux 5.8 (August 2020) onwards, although it would have been fixed in Linux kernel 5.16.11, 5.15.25 and 5.10.102. For more info and the method of exploitation, the vulnerability report is CVE-2022-0847.
But, seriously, do not stress, that it is not worth it. The main GNU/Linux distributions are already preparing their patches for the rest of the affected kernel versions. In addition, it is only exploitable with physical access to the device. There are other variants, although those use less severe vulnerabilities, but allow remote exploitation.
In any case, it may be more complex in the scope of Android. As indicated, mitigation is not possible in Dirty Pipe. It requires an update of the Linux kernel; and sometimes, it takes time for Android to release all of its patches for public.