What is wmiprvse.exe in Windows and is it Safe?
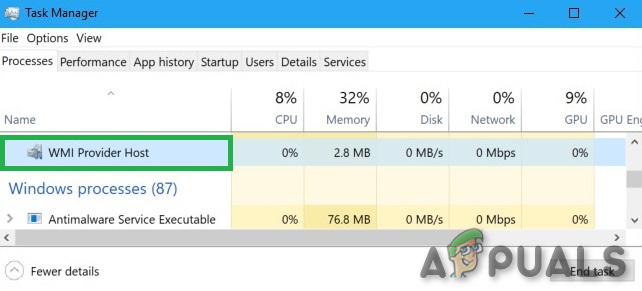
WMIPrvSe.exe or as the description in Task Manager mentions, it is a WMI Provider Host, which is a legitimate background process which runs right after booting up Windows 10, but it’s also found in Windows 7 and 8. It is derived from Windows Management Instrumentation Provider Host Service and the .exe extension is the indication of an executable file.
By this feature, Windows provide a standardized way for administrative scripts & software to request information about the state of the Windows OS and data on it. “WMI Providers” provide this information, when requested. For example, software or commands could find information about the state of BitLocker drive encryption, view entries from the event log, or request data from installed applications that include a WMI provider.
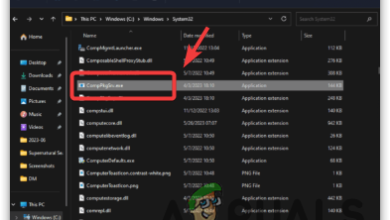
It is particularly useful for enterprises that centrally manage PCs, especially as information can be requested via scripts and shown in a standard way in administrative consoles. With WMI Provider Host, file managers on the enterprise systems are capable of configuring & searching for system information, network and application information in the network. Even on a home system, some installed software may request information about the PC through the WMI Provider Host. Some 3rd party apps use this service to tie into monitoring & management services in Windows. It is located in C:\Windows\System32 by default.
Developers can also use WMI Provider Host to create event monitoring apps that can alert users when important incidents happen. These programs can also notify users about important events related to the file, network or application management right after happening of each event.
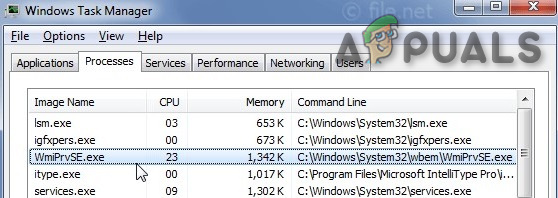
In earlier versions of Windows, providers were loaded in-process with the Windows Management service (WinMgmt.exe), running under the LocalSystem security account. Failure on the part of a provider caused the WMI service to fail and when the next request made to WMI, the service restarted. But from Windows XP, WMI is part of a shared service host with different other services to avoid the stoppage of all the services when a single provider fails, and providers are part of a separate host process named Wmiprvse.exe. Multiple instances of Wmiprvse.exe can run at the same time under different accounts: LocalSystem, NetworkService or LocalService. The core of WMI i.e. WinMgmt.exe is loaded into the Svchost.exe which is a shared Local Service host. When we look through the process tress in Process Explorer it is revealed that WmiPrvSE is part of Microsoft’s Web-Based Enterprise Management (WBEM), the Common Information Model (CIM) & Microsoft Operations Manager (MOM, which is now called as SCOM [System Center Operations Manager.])
MOM (SCOM) is an event and analytics organizer and dispatcher. It handles security permissions, network reliability, diagnostics, data health, report writing, and performance monitoring.
CIM is a set of standards that allow for compliance between elements managed by an IT infrastructure.
WBEM is a system management technology protocol based on Internet standards that tie into the interface of how an application or operating system is managed. WMI is more or less Microsoft’s way of using WBEM.
Web-Based Enterprise Management (WBEM) is a standard by the Distributed Management Task Force (DMTF) which is implemented in Windows as WMI, (a set of extensions to the Windows Driver Model), so that Windows servers and workstations can belong to enterprise networks which use remote infrastructure monitoring and control applications conforming to WBEM and the Common Information Model (CIM). A WMI “provider” routine collects and transmits information to the monitoring application about the performance of a process or the subsystem.
We can also say that, without WmiPrvSE, Windows apps could not be easily managed because the host process that allows the necessary management of services to operate is not functional. Users and administrators would not likely receive notifications when errors occur. In Process Explorer we can see that WmiPrvSE is a child of svchost.exe.
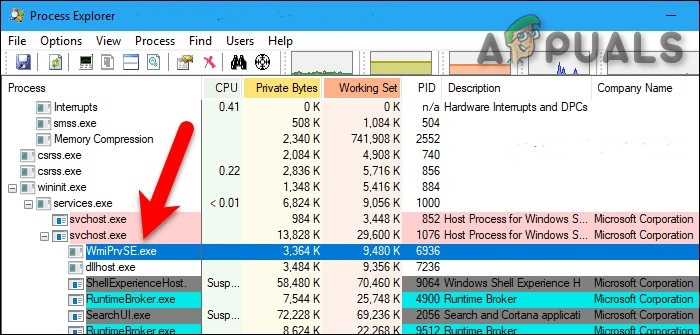
It resides in the “WBEM” subdirectory of “C:\Windows\System32”. It is a core Windows system file and cannot be uninstalled. Multiple instances of it can run at a time, each being a “host” implementing a WMI “provider” routine.
Tasks through programming or scripting languages through WMI daily management can be undertaken e.g. the ability to reboot a computer remotely, manually start a process on a remote system. Also, WMI is capable of views, querying, event creation, and remoting.
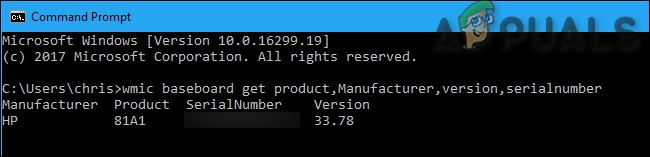
You can also use WMI yourself to find a variety of useful pieces of information that aren’t normally exposed in the Windows interface on your PC. For complete details visit Microsoft WMI command-line tools e.g. in the image below WMIC command is used to know details of PC.
Microsoft also has a list of included WMI providers on its website.
Registry and System File Locations for WmiPrvSE
Undermentioned are registry and system file locations for the Wmiprvse.exe are:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Wbem\CIMOM\CompatibleHostProviders
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Wbem\CIMOM\SecuredHostProviders
HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Classes\CLSID\{1F87137D-0E7C-44d5-8C73-4EFFB68962F2}\LocalServer32
C:\Windows\System32\wbem\WmiPrvSE.exe
WmiPrvSE.exe does not usually use many system resources, but if another process on your system is behaving badly then WmiPrvSE.exe will use a lot of CPU.
WmiPrvSE.exe is Safe or not
WmiPrvSE.exe is needed for Windows to function properly and is a safe process by Microsoft. You should not shut it down or mess with it, but doing so won’t cause a catastrophic failure of the system.
Under normal conditions, WmiPrvSE has a small system footprint and only runs when you first launch Windows. If the process causes problems, it’s likely a poorly written software or a virus may cause the service to push CPU usage to abnormally high levels that can render Windows nearly unresponsive at times. Removal of the faulty app or virus is the answer in solving errors related to Wmiprvse.exe. Remember that before repairing the problem the user will have to disable or halt the WMI process and service firstly.
Hackers create files with virus scripts and name those files/scripts after wmiprvse.exe to spread a virus on the internet.
The wmiprvse.exe is located in the directory C:\WINDOWS\System32\Wbem. And in all other cases, wmiprvse.exe is a virus, spyware, trojan or worm. Check it with your Anti-Virus program.
Check if the PC is infected by wmiprvse.exe malware.
Beware of the following symptoms to see if there is a suspicion that the PC may be infected with wmiprvse.exe malware:
- Fluctuations in Internet connection
- Too much CPU usage by wmiprvse.exe
- PC is very slow
- The browser is redirected to irrelevant websites, automatically.
- Unsolicited ads and popups start appearing
- Screen freezes constantly
Follow the steps below to diagnose the PC for possible malware/virus attack on wmiprvse.exe:
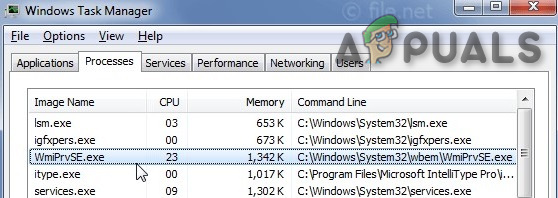
- Press CTRL+ALT+DEL keys to open Task Manager.
- If the file wmiprvse.exe is not located in C:\Windows\System32, then run a full scan of your antivirus program to get rid of the virus/malware.
There are other errors also when trying to install another software
- Exe Application Error.
- exe is not a valid Win32 application.
- exe has encountered a problem and needs to close. We are sorry for the inconvenience.
- Cannot find wmiprvse.exe.
- exe not found.
- Error starting program: wmiprvse.exe.
- exe is not running.
- exe failed.
- Faulting Application Path: wmiprvse.exe.
Then run a full scan of your antivirus program to get rid of the virus/malware. Following are the examples of some malware disguised as Wmiprvse.exe
- Virus: Win32/Virut.BO which was detected by Microsoft.
- 25CU14/TROJ_SPNR.25D514 which was detected by TrendMicro.
Therefore, it is always a good idea to check the WmiPrvSE.exe process on the PC if it is a threat or not.
Best practices for resolving WmiPrvSE issues
A clean & tidy PC is the basic requirement to avoid problems with WmiPrvSE. Follow the under-mentioned steps to make sure you are safe:
- Run cleanmgr
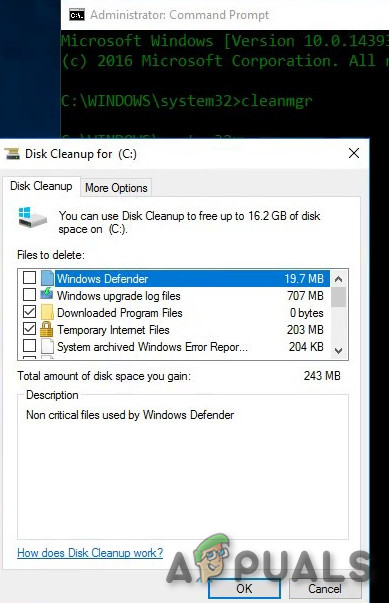
cleanmgr - Then run sfc /scannow,
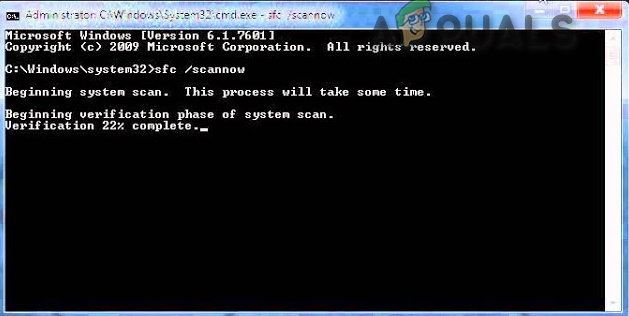
sfc/scannow - Uninstall the programs that are no longer required,
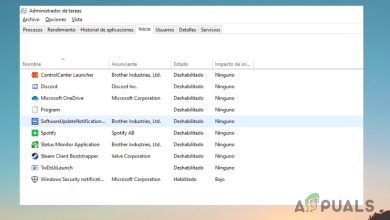
- Check for Autostart apps by using msconfig
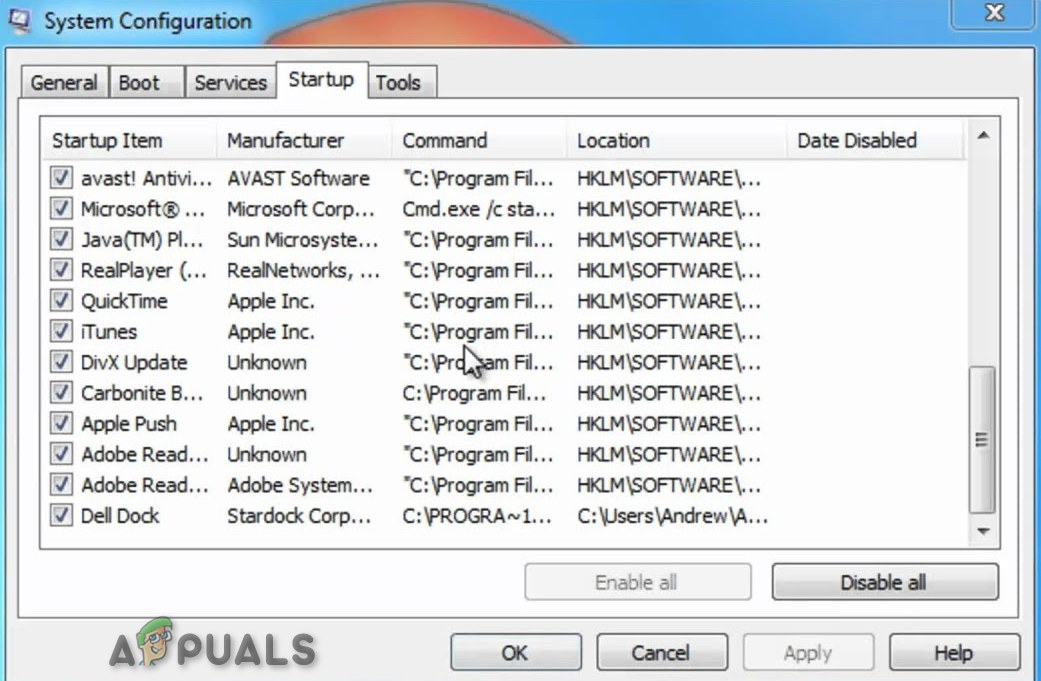
msconfig - Enable Windows’ Automatic Update.
- Perform periodic backups, or set restore points. And if you suffer from a problem, try to remember the last action you did or the last application installed before the appearance of the problem for the first time.
- Use the resmon command for the identification of the processes that are causing problems.
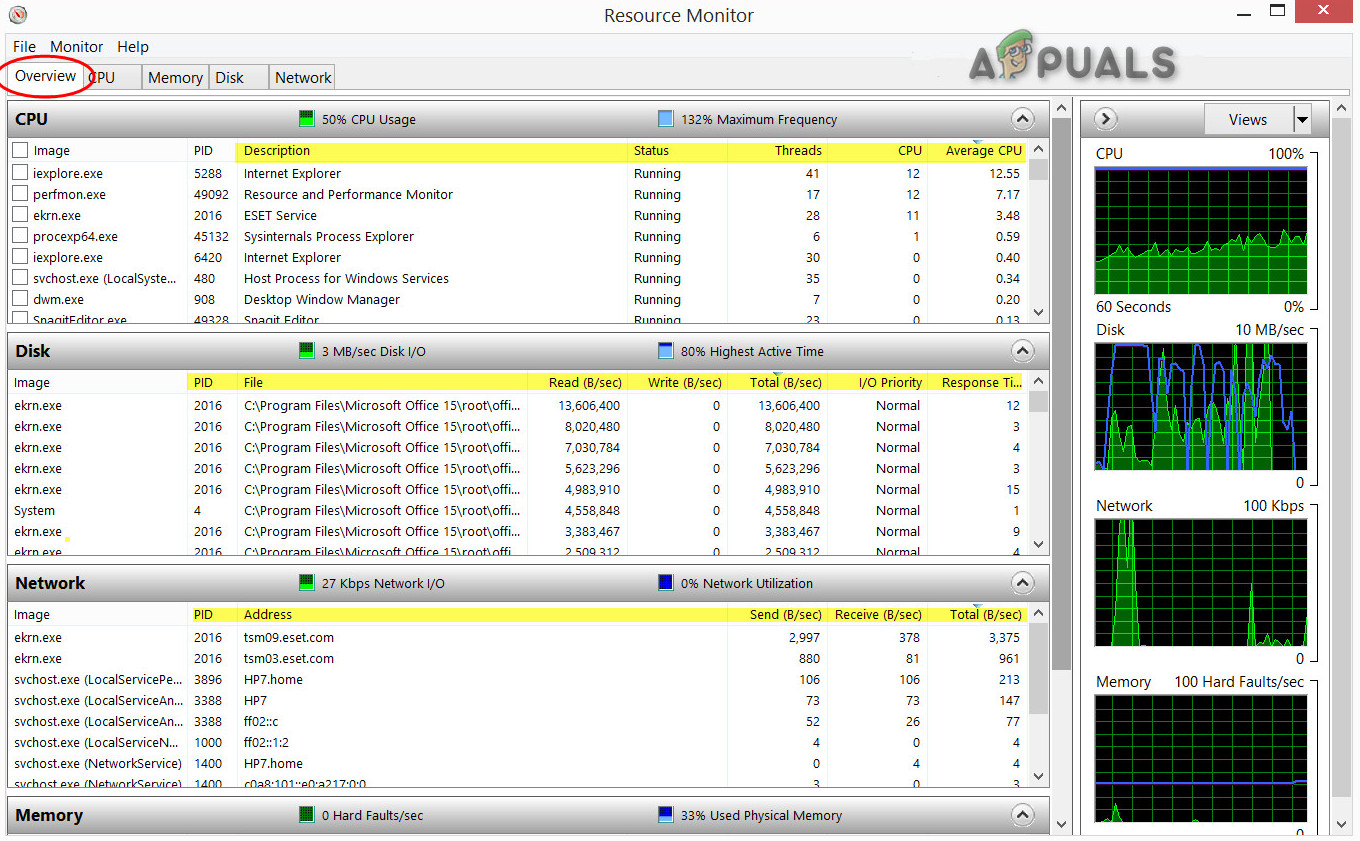
Resource Monitor - Even for the problems serious in nature, try to repair in spite of reinstalling Windows, for Windows 8 & 10, execute the
DISM.exe /Online /Cleanup-image /Restorehealth
command. Which will repair the operating system without loss of any data.
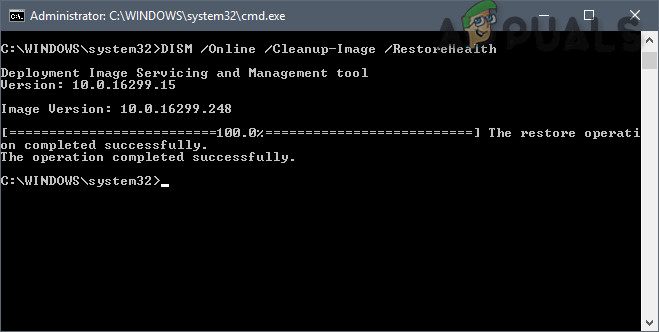
Restore Windows Health