Fix: AADSTS50105 Error in Microsoft Entra ID (Authorization Failure)
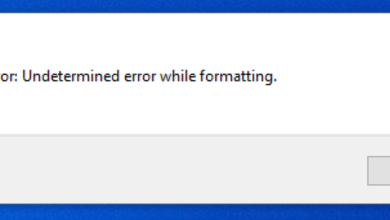
The AADSTS50105 error in Microsoft Entra ID is an authorization failure that occurs when a guest in B2B collaboration attempts to access an Enterprise Application that requires explicit assignment but lacks the necessary role or group membership.
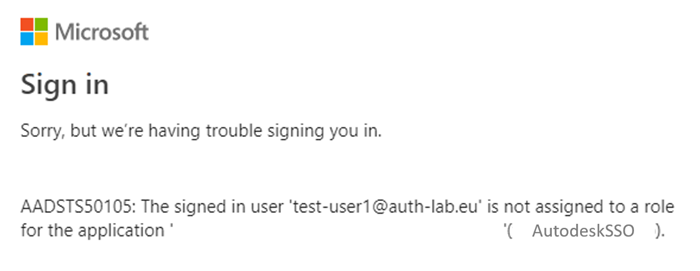
In most cases, the error appears right after a successful SSO authentication. This indicates that the user’s credentials are valid, but they do not have the required permissions. The problem is tied to the “Assignment required” setting, which enforces the principle of least privilege and blocks anyone without explicit access.
While error code 50105 is primarily linked to a missing assignment, other factors can also trigger it. Common examples include:
- Provisioning gaps – incomplete automation or overlooked onboarding steps.
- Policy conflicts – Conditional Access rules or misconfigured enterprise apps.
- Token issues – malformed or expired tokens preventing valid authorization.
- Account restrictions – temporary lockouts after repeated sign-in attempts.
- Network-related blocks – access denied from IP addresses flagged for suspicious activity.
The most direct way to resolve this error is to grant the guest user explicit access to the Enterprise Application in Microsoft Entra ID. Doing so ensures they are provided with the required permissions or role. Since the “Assignment required” setting enforces strict access control, users without an explicit assignment are automatically blocked. By adding the assignment, the authorization requirements are met, allowing the guest user to sign in without further restrictions.
- Open your web browser.
- Navigate to the Microsoft Entra admin center.

- Sign in as a Cloud Application Administrator or Global Administrator.
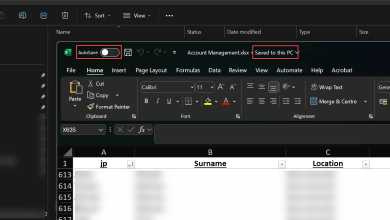
- Go to Identity>Applications>Enterprise applications.

- Search for and select the target application.
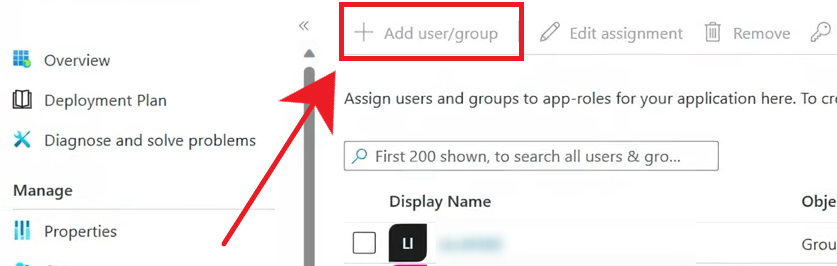
- In the application pane, under the Manage section, click Users and groups.
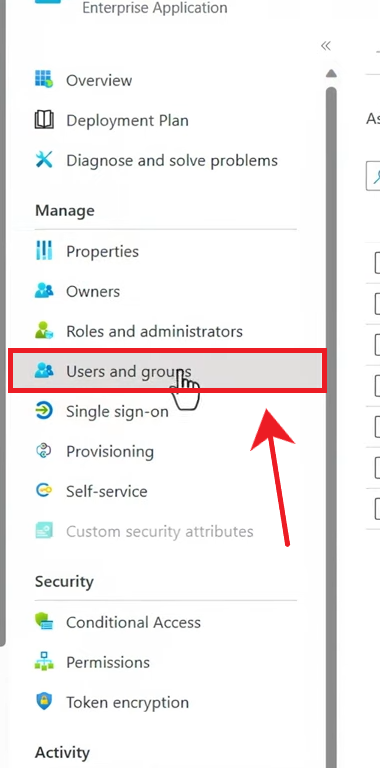
- Click the “+ Add user/group” button.
- On the Add Assignment pane, select None Selected under Users and groups.
- Search for and choose the guest user who requires access (for example, user@abc.com).
- Under Select a role, choose the appropriate app role (for example, Standard user). If the app has no roles, this step can be skipped.
- Click Assign to grant access.
To minimize the risk of this error recurring, organizations should apply several preventive measures:
- Immediately assign guest users to the right groups when they are invited.
- Use security groups and group-based licensing to simplify dynamic access control.
- Run Microsoft Entra ID Access Reviews regularly to remove outdated or unnecessary permissions.
- Enforce MFA for all guest accounts, and configure cross-tenant MFA trust if needed.
- Reduce browser-related issues by clearing the cache or using an incognito session when signing in.